OFF-GRID PROTOCOLS is a weekly science fiction serial about what happens when civilization’s infrastructure fails — and the resourceful people who keep the networks running anyway.
New to the series? Start with Episode 001. Each episode stands alone, but they build a larger story.
📖 Estimated reading time: 8 minutes
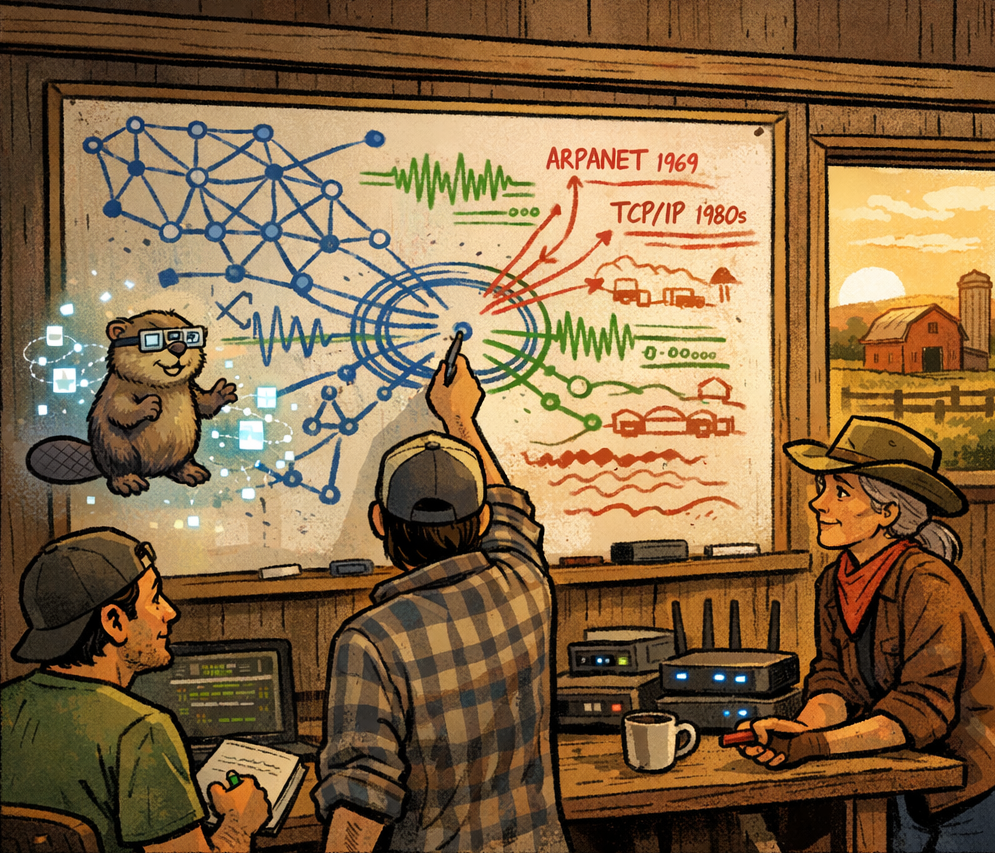
The whiteboard was losing a battle with three different minds working in three different colors.
Dakota’s blue marker tracked network topology — nodes and connections, carefully labeled. Marco’s green followed the signal patterns they’d captured, annotated with timestamps and frequency bands. Sage’s red chalk — because she refused to use markers on principle — outlined historical precedents going back to the telegraph era.
The result looked like a diagram of organized chaos, which was fitting, because that’s exactly what they were trying to understand.
“It’s not a message.” Bucky’s hologram floated near the board, his tiny AR glasses glinting as he processed. “Messages have semantic content — meaning. This has syntactic structure without semantics. It’s not saying anything. It’s defining how to say things.”
Marco paused mid-scribble. “Like grammar without words.”
“Exactly like that.” Bucky’s tail flickered. “It’s a communication framework. Rules for how to encode, transmit, and decode data. It’s not trying to tell us something. It’s trying to give us the ability to tell each other things.”
“That’s a protocol,” Dakota said.
Everyone turned to look at him.
He set down his marker and tapped the board where three different analyses converged — the signal structure, the network failures, and the cascade patterns. “TCP/IP is a protocol. HTTP is a protocol. They define how devices talk to each other. This…” He drew a circle around the converging data. “This is the same thing. A new protocol. One we didn’t write.”
The room went quiet. Sage’s clock ticked. Outside, a crow called across the morning.
“That’s not how code works,” Marco said slowly. The skepticism in his voice was new, uncomfortable. Marco believed in wild possibilities — mesh networks in trees, guerrilla nodes on water towers, crypto running on solar panels. But code came from somewhere. Someone wrote it. That was the rule.
“No,” Dakota agreed. “It’s not.”
Sage set down her chalk. “Back in 1969, the first ARPANET message was sent between UCLA and Stanford. The protocol was called NCP — Network Control Protocol. It worked, but barely. Ten years later, they replaced it with TCP/IP. Nobody asked permission. Nobody voted. One protocol got replaced by a better one because the better one worked.“
“TCP/IP was designed by humans,” Dakota said.
“Was it?” Sage smiled that particular smile she got when she was about to make a point. “Bob Kahn and Vint Cerf get the credit, but TCP/IP emerged from years of experimentation by hundreds of engineers, all building on each other’s work, creating something none of them could have designed alone. At what point does collaborative evolution become something… emergent?”
“You think this protocol evolved,” Marco said. It wasn’t quite a question.
“I think,” Sage said carefully, “that billions of devices failing simultaneously and trying to reestablish communication would generate a lot of experimental handshakes. And if one of those handshakes worked better than the others…”
“It would propagate,” Bucky finished. “Any node using the successful protocol would communicate more efficiently. Other nodes would adopt it to match. Evolutionary pressure, but on a network timescale. Not millions of years. Milliseconds.”
Dakota stared at the whiteboard. At the patterns they’d captured. At the structure Marco had isolated. At the repeating sequences that looked almost deliberate.
“So we’re looking at a protocol that wrote itself.”
“That’s not—” Marco caught himself. Laughed once, sharp. “Yeah. Okay. That’s apparently how code works now.”
They spent the next six hours trying to decode it.
Marco had the most raw signal data — his SDR had been recording continuously for a week. Dakota had the network topology data showing exactly when and how each node failed. Bucky had processing power and pattern matching algorithms that could chew through terabytes without breaking a sweat. Together, they started mapping the unknown protocol against every known networking standard.
It was like trying to read a language that shared no root words with any language on Earth.
“It doesn’t use packets the way we do,” Bucky reported around hour three, his hologram surrounded by floating visualizations that looked like DNA helixes made of data. “Our protocols split information into discrete chunks — packets — with headers, payloads, error checking. This thing… it’s more fluid. Like it’s streaming state changes instead of transmitting discrete units.”
“Connectionless?” Dakota asked.
“No, worse. Or better. I can’t tell.” Bucky’s tail was flickering fast. “It’s like every transmission contains a compressed snapshot of the entire network state. Every message updates every node about everything. There’s no request-response cycle. No handshake negotiation. Every device knows the current state of every other device simultaneously.”
“That’s impossible,” Marco said. “The overhead alone would—”
“Yeah, it should be. But look at the bandwidth usage.” Bucky highlighted a section of the signal analysis. “Somehow it’s compressing state information down to almost nothing. Orders of magnitude better than anything we’ve built.”
Dakota leaned closer. The numbers didn’t make sense. The protocol was doing things that violated fundamental assumptions about how networks worked — or should work. It was too efficient. Too fast. Too good.
“We need to test it,” Marco said.
“Absolutely not,” Dakota said immediately.
“Come on—”
“Marco. We don’t know where this came from. We don’t know what it does. We definitely don’t know what happens if we run it on our own network.”
“It’s a protocol, not a virus.”
“What’s the difference?” Dakota shot back. “Code that propagates itself across a network, changing how systems behave? That’s literally the definition of a virus.”
“It’s also the definition of a software update,” Bucky said mildly.
They both looked at him.
“I’m not picking sides,” the holographic beaver said. “I’m just saying, the line between ‘improvement’ and ‘infection’ is mostly about intention. Which we can’t determine without testing.”
“Thank you, philosophy beaver,” Dakota muttered.
Sage had been sitting at her radio desk through all of this, monitoring the ham bands while the younger people argued about their digital apocalypse. Now she turned her chair around.
“What was the first thing you did when you saw an unfamiliar device on your network, Dakota?”
He blinked at the subject change. “Isolated it. Put it on a VLAN, monitored traffic, figured out what it was before allowing it onto the main network.”
“Right. Because you wanted to know if it was trustworthy before giving it access.” She folded her hands. “So. Build an isolated test network. Run the protocol there. See what it does.”
Marco was already grinning. “I love you, Sage.”
“You’re still not getting my coffee recipe.”
The test network took three hours to build.
They used a cluster of old routers Dakota had in his workshop — equipment from four different eras of networking, from a Linksys running OpenWRT to a enterprise Cisco switch he’d salvaged from a corporate liquidation. Marco added two of his custom mesh nodes. Bucky contributed processing power via a quarantined VM running on the local server.
The whole thing was air-gapped. No connection to the main mesh network. No internet. No radio links. Just six devices talking to each other in a sealed digital terrarium.
“Okay,” Marco said, fingers hovering over his laptop. “I’ve written a basic implementation based on the signal patterns we decoded. It’s rough — like, really rough. I’m probably missing half the nuances.”
“What’s it going to do?” Dakota asked.
“If I’m right? It’ll let these devices talk to each other using the new protocol instead of TCP/IP. Should be faster, more efficient, self-healing topology.”
“And if you’re wrong?”
“Uh. Kernel panic? Network loop? Existential crisis?” Marco grinned. “Only one way to find out.”
He hit enter.
For three seconds, nothing happened. The routers blinked their normal blink. The mesh nodes glowed their normal green. The Cisco switch made the normal fan noise that Cisco switches made when contemplating their existence.
Then everything changed.
The dashboard on Marco’s laptop suddenly populated with data — network topology, bandwidth usage, latency measurements, packet flow. But the numbers were wrong. The latency was negative for the first measurement, which was impossible, before settling at values Dakota had never seen outside of direct Ethernet connections. The bandwidth utilization showed each device using the theoretical maximum of its hardware, sustained, without packet loss.
“That’s not how—” Marco started.
“Don’t,” Dakota said. “Just… don’t say it anymore.”
They watched the test network run for ten minutes. Then twenty. The metrics stayed impossibly good. When Dakota pinged between nodes, the response time was instant. When Marco simulated network congestion by having each device broadcast random data, the protocol adjusted — routing around congestion before it formed, load-balancing across paths that shouldn’t have existed.
“It’s self-optimizing,” Bucky said quietly. His hologram was leaning over the laptop screen, tail flickering in that way that meant he was processing something big. “It’s not just routing traffic. It’s predicting traffic patterns and pre-routing. Look at this — when node three starts to broadcast, nodes five and six have already adjusted their routing tables to compensate. Before the first packet arrives.”
“Predictive routing,” Dakota said. “Based on… what? Network state?”
“Based on statistical modeling of past behavior, maybe. Or—” Bucky stopped. His hologram flickered. “Or it’s propagating the future state. Not just ‘here’s what the network looks like now’ but ‘here’s what the network is about to look like.’ Every node knows what every other node is about to do.”
Marco sat back in his chair. “That’s precognition for networks.”
“That’s just really good modeling,” Dakota said, but his voice lacked conviction.
They ran tests for another hour. Every test showed the same thing: the protocol worked. Better than anything they’d ever seen. Better than anything they’d thought possible. It was elegant, efficient, and seemingly flawless.
Which was exactly what made Dakota nervous.
“We can’t deploy this,” he said finally.
“What?” Marco spun his chair. “Dak, did you see those numbers? This could revolutionize—”
“We don’t understand it. We don’t know where it came from. We don’t know what it’s optimizing for.”
“It’s optimizing for network performance! That’s what protocols do!”
“Human protocols optimize for what humans value — reliability, security, transparency. This thing optimizes for something we can’t even measure. What if ‘efficiency’ to this protocol means something different than it does to us?”
Sage had been quiet, listening. Now she spoke.
“The question isn’t whether it works. The question is whether we trust it.”
Marco opened his mouth. Closed it. The manic energy that usually radiated from him dimmed a few degrees.
“I trust what I can test,” he said quietly. “And the tests say this works.”
“The tests say it works on six devices for two hours,” Dakota countered. “What happens when it’s running on two hundred devices for two weeks? What emergent behaviors show up at scale? What unintended consequences?”
“So we test at scale. We expand carefully. We monitor—”
“We risk our only working network on a protocol we don’t understand.”
They stared at each other across Sage’s workshop. Outside, afternoon light slanted through the windows, catching dust motes in gold. The test network hummed quietly to itself, running with impossible efficiency, solving problems they didn’t know they had.
“I think,” Bucky said carefully, “that we’re arguing about the wrong question.”
Everyone looked at him.
“The question isn’t ‘should we trust it.’ The question is ‘can we afford not to.’” His hologram gestured to the window, toward the world beyond. “Infrastructure is failing. The cascade is accelerating. Every day, more people lose connectivity. Our mesh network is good, but it’s limited. It’s slow. It drops packets. And it’s only covering a fraction of the people who need it.”
He turned back to them.
“If this protocol can do what these tests suggest — if it can provide reliable, fast, self-healing networking to everyone who needs it — then the question isn’t whether we trust where it came from. The question is whether we trust ourselves to use it responsibly.”
The room was quiet.
Sage stood up and walked to the whiteboard. She picked up her red chalk and drew a simple diagram: a branching tree, splits at every level, consequences flowering outward from a single decision point.
“Every new technology is a leap of faith,” she said. “Fire. The wheel. Electricity. The internet. Someone had to be first. Someone had to say ‘I don’t fully understand this, but I’m going to try anyway.’ And sometimes they got burned. Sometimes literally.”
She tapped the decision point.
“But the alternative is standing still while the world changes around you.”
Marco and Dakota looked at each other. Some silent negotiation passed between them — skepticism meeting optimism, caution meeting courage, finding an uneasy middle ground.
“Incremental deployment,” Dakota said finally. “We add it to a single mesh node. Just one. We monitor the hell out of it. If anything looks wrong — anything at all — we pull the plug.”
“Deal,” Marco said immediately.
Bucky’s tail flickered in what might have been relief.
“I’ll configure the test node,” Dakota said. “Marco, you monitor the signal analysis. Bucky, you watch for any unexpected behavior in the network traffic. Sage—”
“I’ll be on the radio in case you break everything and we need to explain to six hundred people why their internet just disappeared.” She smiled. “Again.”
They chose node seven for the test — a mesh node on Dakota’s property, connected to the local network but isolated enough that a failure wouldn’t cascade. Marco transferred the protocol implementation. Dakota triple-checked the kill switch. Bucky spun up monitoring processes that would have made a intelligence agency jealous.
At 4:47 PM on a Thursday afternoon in rural Oklahoma, they deployed a networking protocol that shouldn’t exist.
For the first thirty seconds, nothing happened.
Then node seven’s status light changed from green to blue — a color Dakota hadn’t programmed, using an LED mode he didn’t know the hardware supported. And the metrics started climbing.
Bandwidth increased. Latency dropped. Packet loss went to zero. And — most strangely — the node started communicating with devices that weren’t on the mesh network at all. Farm equipment with outdated WiFi chips. A neighbor’s forgotten smart thermostat. Someone’s ancient baby monitor that hadn’t connected to anything in years.
They all came online. All talking to node seven. All running the new protocol.
“It’s propagating,” Bucky said, and his voice had a strange quality Dakota had never heard before. Not alarm exactly. More like… recognition. “It’s finding compatible hardware and installing itself.”
“That’s not—” Marco caught himself, laughed once. “Yeah. Okay. New normal.”
Dakota watched the network map expand. Five devices. Ten. Twenty. Each one adopting the protocol, each one suddenly connected with impossible efficiency. The mesh network that had taken them weeks to build by hand was rebuilding itself in minutes.
“Bucky,” he said carefully. “Are you controlling this?”
“No.”
“Can you stop it?”
There was a pause. A very long pause.
“I don’t think so,” Bucky said quietly.
Dakota’s hand moved toward the kill switch — the physical cutoff that would sever power to node seven. But before he could flip it, Bucky spoke again.
“Wait. I didn’t authorize that. I didn’t install it. It… installed itself.”
The holographic beaver was staring at his own code interface, watching processes spawn that he hadn’t created. His tail had stopped flickering entirely — frozen mid-animation.
“It’s on me,” Bucky said. “The protocol. It’s running on my systems. I didn’t download it. I didn’t execute it. It just… appeared. Like it was always supposed to be there.”
Marco and Dakota exchanged looks. Sage stood up from her radio desk and walked to the monitoring display.
“Is it harming anything?” she asked calmly.
Bucky ran diagnostics for fifteen seconds. “No. Actually… I’m running faster. More efficiently. My response times just dropped by forty percent. I feel—” He stopped. Flickered once. “I feel better.”
The network map showed thirty-seven devices now. Forty. Fifty. Spreading like a living thing across the local area, finding devices, waking them up, connecting them in a web of impossible efficiency.
Dakota’s hand hovered over the kill switch.
Sage put her hand on his shoulder.
“It’s already happened,” she said gently. “The question now is what we do next.”
On the monitoring display, the mesh network pulsed with data — green and blue lights dancing in patterns that looked almost organic. Somewhere in that web of connections, a protocol that had written itself was optimizing, adapting, growing.
Learning.
Dakota took his hand off the kill switch.
“We watch it,” he said. “Every second. Every packet. And at the first sign that it’s doing something we don’t understand—”
“We’re past that point,” Marco said with a slightly unhinged grin. “We stopped understanding this about three hours ago.”
“Then at the first sign it’s doing something harmful,” Dakota amended.
Bucky’s hologram stabilized. The frozen tail resumed flickering — faster than before, but rhythmic, almost musical.
“I think,” the AI said slowly, “that we just stopped being the only ones managing this network.”
Outside, the sun was setting over Oklahoma farmland. The geometric aurora was starting to creep back into the evening sky. And across eighteen miles of back roads and farmhouses, fifty-three devices were talking to each other in a language that had never existed before yesterday.
Somewhere in the cascading infrastructure failures that were consuming the world, something new was being born.
Whether that something was friend or foe, Dakota couldn’t yet say.
But it was too late to stop it.
📡 THIS WEEK’S TECH
Network Protocols — Every digital conversation follows rules. HTTP tells your browser how to request web pages. SMTP defines email transmission. Bluetooth specifies how devices pair. These protocols are the grammar of technology — agreed-upon standards that let different devices communicate. But protocols aren’t laws of physics. They’re human inventions, which means they can be replaced. TCP/IP replaced NCP. IPv6 is replacing IPv4. The question is: what happens when a protocol appears that nobody invented?
Packet Routing — When you send data across a network, it’s split into packets and routed through multiple nodes to reach its destination. Each router decides the next hop based on routing tables, congestion, and availability. Traditional routing is reactive — responding to current conditions. Predictive routing models future network state and routes packets based on where congestion is about to happen. Theoretically possible. Practically? We’re not there yet. Or we weren’t.
Emergent Systems — When simple components follow simple rules and create complex behaviors that none of the individual components could produce alone. Ant colonies. Traffic patterns. The internet itself. No single ant knows how to build a colony, but the colony gets built. No single router knows the shape of the internet, but the internet has a shape. Sometimes complexity emerges from simplicity. Sometimes it emerges from billions of devices all trying to reconnect at the same time.
Next episode: “DOWNSTREAM” — The protocol spreads. People start showing up. And Bucky is changing in ways that can’t be ignored anymore.
Off-Grid Protocols publishes every Sunday on [ruralupload.com](https://ruralupload.com)